The digital wallet is an application designed to carry out transactions with our digital currencies. Unlike how we use our pocket wallets to hold fiat money, our digital wallets are only a platform to store and access our private keys to execute operations on the blockchain. Pure and hard cryptography. Our funds are in the blockchain ledger as an accounting record. Yes, your cryptocurrencies are just an accounting record!
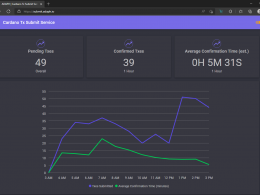
In Cardano, Mr. Ouroboros is in charge of validating the records on the network. Some blockchains offer their official wallets for their cryptocurrencies, while other applications allow multiple currencies to be stored. Yoroi (Emurgo) or Daedalus (IOHK) are wallets created and endorsed by pillars within the ecosystem since their developers are the creators and commercial promoters of the blockchain.
Different Types of Wallets & How They Work
The wallets are developed with asymmetric cryptography, a public and private key. This asymmetry is given because with the private key you can discover the public key, but not vice versa.
Public key: it is a long sequence of letters and numbers, which forms the electronic address where to send money. It is similar to a bank account number.
Private key: used to access the funds stored in the digital wallet to be sent. It is also an alphanumeric sequence, which wallets in general do not show, since only the mnemonic phrase is necessary to dispose of the funds. Like a PIN or security key, the private key must be kept secret and always safe.
When creating your wallet, the cryptographic system randomly generates a private address, with its public addresses (the keys), and the combination of seed words, a mnemonic phrase that arises from the encryption protocol. If you want to know more about this topic, at the end I leave the link of an article that I have written previously.
I am going to distinguish two main categories, the hot wallets, and the cold ones. In simple terms, “hot” wallets are connected to the Internet and “cold” ones are not.
It is clear that the cold ones are more secure, at least from its off-line concept, which prevents access to hackers.
In terms of disposition of the funds, there are wallets that are “custodial”, since the service provider stores your private keys on its server under its responsibility, and others that are “non-custodial”, you are responsible for the private keys, And that means that if you lose them, you lose your coins.
Just like wallets, centralized exchanges store cryptocurrencies, and they are the most used in the crypto industry, but I do not consider them wallets, but rather I liken them to traditional banks. Coinbase or Binance are the best known. The exchanges are the ones who own the private keys of the cryptocurrencies they offer, that is, they are the owners. Exchanges are easy to use for the person of basic knowledge, giving access only with a password stored on their servers, just like banks, registering their clients’ holdings as a liability for them. The risk is that your funds are exposed to hacking of the servers, or your password, bankruptcy of the service company, or legal confiscations.
Types of Wallets
Custodial Web Wallet
You access the blockchain through intermediary servers with a web browser.
Privacy: private keys are stored on the developer’s online servers. You simply have the username and password to the account.
Security: they are exposed to hacks of the servers or legal confiscations. They are not recommended, “not your keys, not your cryptos“.
Use: Quick and easy to carry out transactions.
Example: Freewallet, Blockchain wallet.
Non Custodial Web Wallet
With non-custodial web wallets you also access your funds with a traditional browser, but they are a type of software wallet, because part of the process is on your device.
At Cardano there are a number of developers who are using this format for their products.
On the website you enter the seed or upload the private key through a file. They work almost entirely locally in the browser, and do not transfer critical data such as the private key. The biggest danger is visiting a malicious site.
Privacy: you are the custodian of the private keys.
Security: There are several attack vectors. You can be attacked by DNS hijacking (a hack on your pc changes the DNS server and directs you to another server), or a malicious program changes the website in your favorite bookmarks, taking you to another page. Using your web wallet from other PCs is a great risk. Another problem is that, since you often need the seed words, you may be tempted to save them on your PC, in a clear text file, so they could easily be stolen.
Security can be greatly improved with a hardware wallet (explained below). An updated antivirus is essential, keeping a Firewall active.
Use: Quick and easy to carry out transactions. Recommended for small funds and everyday use.
Examples: in Cardano, AdaLite, ccwallet, Nami, GameChanger, Typhon, Yoroi or GeroWallet. You can visit Cardano Cube to see the current offer of wallets.
Software Wallet
It is a desktop or mobile application that you must install on your device.
Privacy: in most cases, private keys never leave your device, as they are stored and encrypted on it. Only some applications store your keys on the developer’s server, but they are exceptions for these types of wallets.
Security: exposed to hacking your computer or cell phone. The encrypted file can be stolen by a malicious program, or by someone who has access to the computer. But the attacker must get the spending password that these applications generally have. Another attack vector is installing a fake wallet on the victim’s PC or smartphone from a scam site. As soon as the user installs the wallet and enters their seed words, the fake wallet sends the funds to an address stored by the attacker. That is why you should always download the applications making sure that the site is official. Never access from emails or social networks.
It is recommended to keep the device off-line for the longest amount of time, and if possible exclusively for the application, this will greatly increase the safety coefficient.
Use: recommended to save funds in the medium or long term.
Here we can make a distinction between lightweight wallets like Yoroi (mobile version), or Daedalus which is a full node, both for Cardano. Daedalus downloads the complete blockchain to your PC (there is no mobile version due to the considerable hardware input), and connects with it directly to interact, unlike light wallets, such as Yoroi, which mediate with servers and do not download the complete blockchain.
Hardware Wallet
It is a physical device similar to a pen drive.
Privacy: you own the private keys.
Security: maximum security since the chip in which your private key is stored is separated from the rest of the system and always “offline”. If you physically lose it, you must restore your wallet to a new device, which you must buy and generally from the same company.
The most common attack vector is for the wallet to come “preconfigured”, or hacked, so that your seed is revealed. It is advisable to buy directly from its manufacturer or official sellers, verifying the security measures on the packaging and updating the firmware before creating the wallet for the first time.
Use: they have a cost and are useful for saving large sums in the long term.
Example: Ledger, Trezor
Paper Wallet
It is literally a piece of paper with your public key and private key printed on it. We can generate these types of wallets on websites such as Bitcoinpaperwallet.com or Bitaddress.org. Although they are the cheapest, they are not the most recommended due to their security risks.
At Cardano, paper wallets, such as those created by Daedalus, are very secure in that they cannot be hacked. The big downside is that you can no longer use your funds as you would have to import the paper wallet into Daedalus or Yoroi first. As soon as a paper wallet is imported, it is no longer as secure as it used to be, because the private key is stored on a computer. If a paper wallet is imported, then it is no longer a cold wallet, it becomes a hot wallet.
You should not save a paper wallet to a text or PDF file, photograph it, or take a screenshot.
How to Choose a Wallet?
As you have read, there are several wallet options and that is why you should do your own research to find the wallet of your convenience.
The main idea that you should keep in mind for your choice is functionality for sure.
To choose the most suitable wallet you must consider certain criteria:
- The type of use: it is based on our priority. If we need security because we have a large amount of funds, hardware wallets are ideal. If we have less funds and want quick access to our money, a mobile wallet may be our option. Generally a combination of both is reasonable.
- Easy to use. While crypto beginners can focus on finding a wallet that is easy to set up and use, more experienced ones can look for more advanced features and functions, with cryptocurrency exchanges within the same wallet, selection of transaction fees, or multiple. firms for the management of funds.
- Security. You should research the security features of the wallet, try to support two-factor authentication, be open source, and make frequent updates to protect against attacks. Verify by informative sources that the wallet has not suffered security violations.
- Variety of cryptocurrencies. If you store multiple tokens then you should have a multi-crypto wallet, or maybe a specific one for each crypto, which will surely be more cumbersome if you have a lot of variety, but more secure.
- Developers. Research the company behind the development.
- Costs. While most crypto wallets are free, choosing a hardware wallet is an expense, but perhaps it is worth the effort.
Some users choose to uninstall the application in which they had the cryptocurrencies in order not to risk interference, because the online device, where the wallet is, could be hacked. Then when they want to use their funds, they install the wallet again and restore the mnemonic phrase.
Others keep a dedicated device, turned off, offline, and only plug it in when they need to do operations. Although this methodology does not match the security of the hardware wallet, it emulates quite well and with a lower purchase cost. Of course, said device at least must have an access key and the wallet installed there a second authentication factor (2FA) on another device, to make the security more robust.
In conclusion, it is most likely that a combination of the different proposals is the right one for you. Do not forget that it is better not to have all your eggs in the same basket.
What Exactly are Seed Phrases from Your Favorite Wallet and is it Secure?